1. 简介
Private Service Connect (PSC) 网络端点组 (NEG) 支持将内部 HTTPS 负载平衡器与外部 HTTPS 负载平衡器链接起来。这可使用客户定义的范围,为本地提供分布式健康检查和数据平面流量。此外,此拓扑还支持通过多个区域性互连将多个 VPC 连接到本地。
在此 Codelab 中,我们将演示如何根据以下拓扑配置此端到端设置。从左到右,本地客户拥有一个用于模拟 HTTP 服务的虚拟机,利用混合连接(高可用性 VPN 或 InterConnect)和混合 NEG 通过内部 HTTPS 负载平衡器公开服务。PSC 使用内部 HTTPS 负载平衡器作为服务连接。PSC NEG 将附件用作后端服务,并向外部 HTTPS 负载平衡器公开。互联网用户可以使用 Google 全球网络来加速对本地 HTTP 服务的访问。
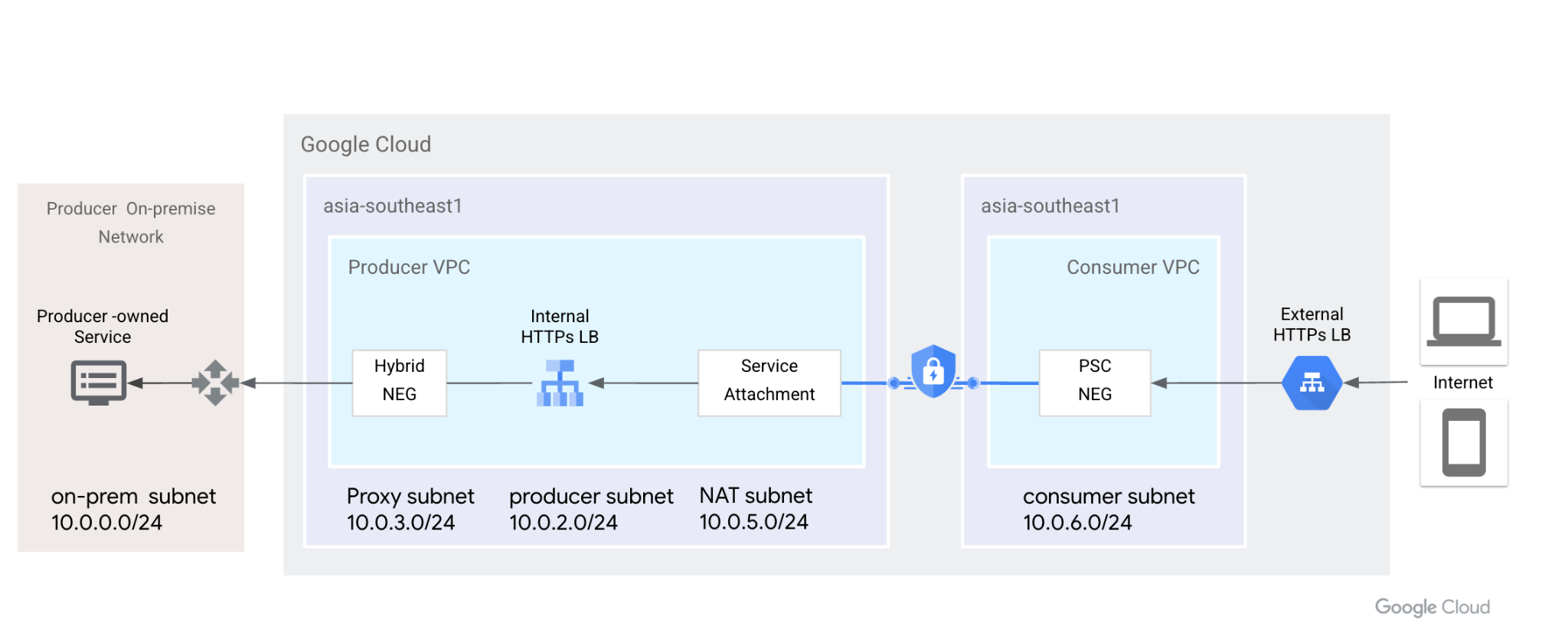
图 1. Private Service Connect 使用网络端点组和服务连接将外部 HTTPS 负载平衡器连接到内部 HTTPS 负载平衡器,并将后端扩展到本地。
学习内容
- 具有混合 NEG 和分布式健康检查的内部 HTTPS 负载平衡器
- 具有内部 HTTPS 负载平衡器的 PSC 服务附件
- PSC 网络端点组设置
- 通过外部 HTTPS 负载平衡器公开 PSC NEG
所需条件
- 了解混合连接(例如高可用性 VPN)
- 了解内部/外部 HTTPS 负载均衡
- Private Service Connect 知识
2. 准备工作
注意:此 Codelab 提供的配置和验证步骤基于图示拓扑,请根据需要修改流程,以满足贵组织的要求。IAM 权限不在本实验范围内。
Codelab 将使用一个项目来模拟整个流程。还支持多个项目。
单个项目 - 更新项目以支持提供方和使用方网络
在 Cloud Shell 中,确保项目 ID 已设置
gcloud config list project gcloud config set project [YOUR-PROJECT-NAME] prodproject=YOUR-PROJECT-NAME echo $prodproject
3. 创建本地资源
在下一部分中,我们将设置本地 VPC 和虚拟机,以模拟客户的本地服务。
VPC 网络
从 Cloud Shell
gcloud compute networks create vpc-demo-onprem --project=$prodproject --subnet-mode=custom
创建子网
从 Cloud Shell
gcloud compute networks subnets create vpc-demo-onprem-asia-southeast1 --project=$prodproject --range=10.0.0.0/24 --network=vpc-demo-onprem --region=asia-southeast1
创建防火墙规则。
内部 HTTPS 负载平衡器支持分布式健康检查,防火墙规则只需允许代理子网 IP 地址范围。按照文档将您的项目列入许可名单。
在 Cloud Shell 中,创建防火墙规则以启用来自代理子网的后端健康检查和数据平面流量。
gcloud compute firewall-rules create vpc-demo-health-checks --allow tcp:80,tcp:443 --network vpc-demo-onprem --source-ranges 10.0.3.0/24 --enable-logging
在 Cloud Shell 中创建防火墙规则,以允许 IAP 连接到您的虚拟机实例,
gcloud compute firewall-rules create psclab-iap-prod --network vpc-demo-onprem --allow tcp:22 --source-ranges=35.235.240.0/20 --enable-logging
4. 创建本地虚拟机实例
此虚拟机模拟本地服务,需要使用混合 NEG 通过内部 HTTPS 负载平衡器公开。
通过 Cloud Shell 创建实例 www01
gcloud compute instances create www01 \
--zone=asia-southeast1-b \
--image-family=debian-11 \
--image-project=debian-cloud \
--network-interface=network-tier=PREMIUM,nic-type=GVNIC,stack-type=IPV4_ONLY,subnet=vpc-demo-onprem-asia-southeast1 \
--shielded-secure-boot \
--shielded-vtpm \
--shielded-integrity-monitoring \
--metadata=startup-script='#! /bin/bash
sudo apt-get update
sudo apt-get install nginx -y
vm_hostname="$(curl -H "Metadata-Flavor:Google" \
http://169.254.169.254/computeMetadata/v1/instance/name)"
filter="{print \$NF}"
vm_zone="$(curl -H "Metadata-Flavor:Google" \
http://169.254.169.254/computeMetadata/v1/instance/zone \
| awk -F/ "${filter}")"
echo "Page on $vm_hostname in $vm_zone" | \
tee /var/www/html/index.nginx-debian.html
sudo systemctl restart nginx'
在下一部分中,我们将使用 letsencrypt 生成证书并将其安装在 Nginx 上。下载公钥和私钥文件,以便执行下一步。您需要暂时向互联网开放 TCP 端口 80,以便生成证书。
确保此虚拟机的域名可公开解析。例如,在 Cloud DNS 中添加一条 A 记录 [www01.yinghli.demo.altostrat.com](http://www01.yinghli.demo.altostrat.com) 并指向虚拟机公共 IP 地址。
gcloud dns --project=$prodproject record-sets create www01.yinghli.demo.altostrat.com. --zone="yinghli-demo" --type="A" --ttl="300" --rrdatas="34.87.77.186"
在虚拟机 www01 控制台中,按照指南在 Nginx 上安装证书,并复制 fullchain.pem 和 private.pem 以供后续步骤使用。
sudo apt install snapd sudo snap install core; sudo snap refresh core sudo snap install --classic certbot sudo ln -s /snap/bin/certbot /usr/bin/certbot sudo certbot --nginx
5. 创建提供方 VPC 网络
注意:此配置不包含混合网络配置。
VPC 网络
从 Cloud Shell
gcloud compute networks create vpc-demo-producer --project=$prodproject --subnet-mode=custom
创建子网
从 Cloud Shell
gcloud compute networks subnets create vpc-demo-asia-southeast1 --project=$prodproject --range=10.0.2.0/24 --network=vpc-demo-producer --region=asia-southeast1
创建代理子网
从 Cloud Shell
gcloud compute networks subnets create proxy-subnet-asia-southeast1 \ --purpose=REGIONAL_MANAGED_PROXY \ --role=ACTIVE \ --region=asia-southeast1 \ --network=vpc-demo-producer \ --range=10.0.3.0/24
混合连接
按照 Cloud VPN 文档在本地 VPC 和 Producer VPC 之间实现高可用性 VPN 连接。在 Cloud Router 上保留默认配置,我们无需将 130.211.0.0/22、35.191.0.0/16 添加到 BGP 通告中。
6. 创建提供方混合 NEG
创建混合网络端点组,并将本地虚拟机的 IP:PORT 添加到 NEG 中。
从 Cloud Shell
gcloud compute network-endpoint-groups create on-prem-service-neg \
--network-endpoint-type=NON_GCP_PRIVATE_IP_PORT \
--zone=asia-southeast1-b \
--network=vpc-demo-producer
gcloud compute network-endpoint-groups update on-prem-service-neg \
--zone=asia-southeast1-b \
--add-endpoint="ip=10.0.0.2,port=443"
7. 创建生产者内部 HTTPS 负载平衡器
目前,外部 HTTPS 负载平衡器仅支持 HTTPS 协议到 PSC NEG(文档)。发布服务时,我们需要使用内部 HTTPS 负载平衡器并启用转发规则全球访问权限。
在 Cloud Shell 中创建区域健康检查。
gcloud compute health-checks create https on-prem-service-hc \
--region=asia-southeast1 \
--use-serving-port
在 Cloud Shell 中创建后端服务并添加混合 NEG。
gcloud compute backend-services create on-premise-service-backend \ --load-balancing-scheme=INTERNAL_MANAGED \ --protocol=HTTPS \ --region=asia-southeast1 \ --health-checks=on-prem-service-hc \ --health-checks-region=asia-southeast1 gcloud compute backend-services add-backend on-premise-service-backend \ --network-endpoint-group=on-prem-service-neg \ --network-endpoint-group-zone=asia-southeast1-b \ --region=asia-southeast1 \ --balancing-mode=RATE \ --max-rate-per-endpoint=100
在 Cloud Shell 中创建网址映射
gcloud compute url-maps create on-premise-url \
--default-service on-premise-service-backend \
--region=asia-southeast1
在 Cloud Shell 中创建区域性 SSL 证书。从虚拟机下载两个证书文件。
gcloud compute ssl-certificates create www01 \
--certificate=fullchain.pem \
--private-key=private.pem \
--region=asia-southeast1
通过 Cloud Shell 创建 https-target-proxy
gcloud compute target-https-proxies create on-premise-httpsproxy \
--ssl-certificates=www01 \
--url-map=on-premise-url \
--url-map-region=asia-southeast1 \
--region=asia-southeast1
在 Cloud Shell 中,预留内部静态 IP 并创建转发规则
gcloud compute addresses create ilbaddress \
--region=asia-southeast1 \
--subnet=vpc-demo-asia-southeast1 \
--addresses=10.0.2.100
gcloud compute forwarding-rules create https-ilb-psc \
--load-balancing-scheme=INTERNAL_MANAGED \
--network=vpc-demo-producer \
--subnet=vpc-demo-asia-southeast1 \
--address=ilbaddress \
--ports=443 \
--region=asia-southeast1 \
--target-https-proxy=on-premise-httpsproxy \
--target-https-proxy-region=asia-southeast1
--allow-global-access
8. 创建 Producer 虚拟机实例
创建提供方虚拟机以进行验证。
从 Cloud Shell
gcloud compute instances create test01 \
--zone=asia-southeast1-b \
--image-family=debian-11 \
--image-project=debian-cloud \
--network-interface=network-tier=PREMIUM,nic-type=GVNIC,stack-type=IPV4_ONLY,subnet=vpc-demo-asia-southeast1 \
--shielded-secure-boot \
--shielded-vtpm \
--shielded-integrity-monitoring
如需允许 IAP 连接到您的虚拟机实例,请创建一个防火墙规则,该规则应:
从 Cloud Shell
gcloud compute firewall-rules create psclab-iap-prod --network vpc-demo-producer --allow tcp:22 --source-ranges=35.235.240.0/20 --enable-logging
从提供方虚拟机控制台访问 [www01.yinghli.demo.altostrat.com](https://www01.yinghli.demo.altostrat.com) 并解析内部 HTTPS 负载平衡器 IP 地址。HTTP 200 表示配置按预期运行。
curl -v --resolve www01.yinghli.demo.altostrat.com:443:10.0.2.100 https://www01.yinghli.demo.altostrat.com * Added www01.yinghli.demo.altostrat.com:443:10.0.2.100 to DNS cache * Hostname www01.yinghli.demo.altostrat.com was found in DNS cache * Trying 10.0.2.100:443... * Connected to www01.yinghli.demo.altostrat.com (10.0.2.100) port 443 (#0) * ALPN, offering h2 * ALPN, offering http/1.1 * successfully set certificate verify locations: * CAfile: /etc/ssl/certs/ca-certificates.crt * CApath: /etc/ssl/certs * TLSv1.3 (OUT), TLS handshake, Client hello (1): * TLSv1.3 (IN), TLS handshake, Server hello (2): * TLSv1.3 (IN), TLS handshake, Encrypted Extensions (8): * TLSv1.3 (IN), TLS handshake, Certificate (11): * TLSv1.3 (IN), TLS handshake, CERT verify (15): * TLSv1.3 (IN), TLS handshake, Finished (20): * TLSv1.3 (OUT), TLS change cipher, Change cipher spec (1): * TLSv1.3 (OUT), TLS handshake, Finished (20): * SSL connection using TLSv1.3 / TLS_AES_256_GCM_SHA384 * ALPN, server accepted to use h2 * Server certificate: * subject: CN=www01.yinghli.demo.altostrat.com * start date: Jun 4 10:36:43 2023 GMT * expire date: Sep 2 10:36:42 2023 GMT * subjectAltName: host "www01.yinghli.demo.altostrat.com" matched cert's "www01.yinghli.demo.altostrat.com" * issuer: C=US; O=Let's Encrypt; CN=R3 * SSL certificate verify ok. * Using HTTP2, server supports multi-use * Connection state changed (HTTP/2 confirmed) * Copying HTTP/2 data in stream buffer to connection buffer after upgrade: len=0 * Using Stream ID: 1 (easy handle 0x55865ef982e0) > GET / HTTP/2 > Host: www01.yinghli.demo.altostrat.com > user-agent: curl/7.74.0 > accept: */* > * TLSv1.3 (IN), TLS handshake, Newsession Ticket (4): * TLSv1.3 (IN), TLS handshake, Newsession Ticket (4): * old SSL session ID is stale, removing * Connection state changed (MAX_CONCURRENT_STREAMS == 100)! < HTTP/2 200 < server: nginx/1.18.0 < date: Mon, 05 Jun 2023 02:29:38 GMT < content-type: text/html < content-length: 35 < last-modified: Sun, 04 Jun 2023 09:02:16 GMT < etag: "647c5318-23" < accept-ranges: bytes < via: 1.1 google < Page on www01 in asia-southeast1-b * Connection #0 to host www01.yinghli.demo.altostrat.com left intact
注意:您无法直接访问虚拟机 10.0.0.2 HTTPS 服务,因为本地防火墙仅允许代理子网 10.0.3.0/24 进行访问。
9. 创建 PSC NAT 子网
从 Cloud Shell
gcloud compute networks subnets create psc-nat-subnet \ --network=vpc-demo-producer \ --region=asia-southeast1 \ --range=10.0.5.0/24 \ --purpose=private-service-connect
10. 创建 HTTPS 服务连接
在 Cloud Shell 中创建 HTTPS 服务附件
gcloud compute service-attachments create ilbserviceattach \ --region=asia-southeast1 \ --producer-forwarding-rule=https-ilb-psc \ --connection-preference=ACCEPT_AUTOMATIC \ --nat-subnets=psc-nat-subnet
验证 HTTPS 服务连接
gcloud compute service-attachments describe ilbserviceattach --region asia-southeast1
记录服务连接名称:
projects/<project>/regions/asia-southeast1/serviceAttachments/ilbserviceattach
11. 创建使用方 VPC 网络
在下文中,使用方 VPC 是在同一项目中配置的,但我们也支持在不同项目中配置。使用方网络与提供方网络之间的通信是通过提供方网络中定义的服务连接实现的。
VPC 网络
从 Cloud Shell
gcloud compute networks create vpc-demo-consumer --project=$prodproject --subnet-mode=custom
创建子网
从 Cloud Shell
gcloud compute networks subnets create consumer-subnet --project=$prodproject --range=10.0.6.0/24 --network=vpc-demo-consumer --region=asia-southeast1
12. 创建 PSC 网络端点组
创建 PSC NEG
复制之前的 HTTPS 服务连接名称,并粘贴到参数 --psc-target-service 中
从 Cloud Shell
gcloud beta compute network-endpoint-groups create consumerpscneg \ --project=$prodproject \ --region=asia-southeast1 \ --network-endpoint-type=PRIVATE_SERVICE_CONNECT \ --psc-target-service=projects/<project>/regions/asia-southeast1/serviceAttachments/ilbserviceattach \ --network=vpc-demo-consumer \ --subnet=consumer-subnet
成功设置 PSC NEG 后,在界面中,依次选择 Private Service Connect -> Published Services -> 注意到已发布的 ilbserviceattach 连接现在指示 1 条转发规则。

13. 创建 Consumer 外部 HTTPS 负载平衡器
创建外部 HTTPS 负载平衡器,并使用 PSC NEG 作为后端服务(文档)。
从 Cloud Shell
gcloud compute addresses create httpspsclb \
--ip-version=IPV4 --global
gcloud compute backend-services create consumer-bs \
--load-balancing-scheme=EXTERNAL_MANAGED \
--protocol=HTTPS \
--global
gcloud compute backend-services add-backend consumer-bs \
--network-endpoint-group=consumerpscneg \
--network-endpoint-group-region=asia-southeast1 \
--global
gcloud compute url-maps create consumer-url \
--default-service=consumer-backend-service \
--global
gcloud compute ssl-certificates create wwwglobal \
--certificate=fullchain.pem \
--private-key=private.pem \
--global
gcloud compute target-https-proxies create consumer-url-target-proxy \
--url-map=consumer-url \
--ssl-certificates=wwwglobal
gcloud compute forwarding-rules create consumer-url-forwarding-rule \
--load-balancing-scheme=EXTERNAL_MANAGED \
--network-tier=PREMIUM \
--address=httpspsclb \
--target-https-proxy=consumer-url-target-proxy \
--ports=443 \
--global
更新 www01.yinghli.demo.altostrat.com 的 DNS 记录,并指向外部 HTTPS 负载平衡器公共 IP 地址
gcloud dns --project=$prodproject record-sets update www01.yinghli.demo.altostrat.com. --type="A" --zone="yinghli-demo" --rrdatas="34.102.178.214" --ttl="300"
14. 验证
在笔记本电脑上,使用 curl 访问 https://www01.yinghli.demo.altostrat.com。
curl -v https://www01.yinghli.demo.altostrat.com * Trying 34.102.178.214:443... * Connected to www01.yinghli.demo.altostrat.com (34.102.178.214) port 443 (#0) * ALPN: offers h2,http/1.1 * TLSv1.3 (OUT), TLS handshake, Client hello (1): * TLSv1.3 (IN), TLS handshake, Server hello (2): * TLSv1.3 (IN), TLS handshake, Encrypted Extensions (8): * TLSv1.3 (IN), TLS handshake, Certificate (11): * TLSv1.3 (IN), TLS handshake, CERT verify (15): * TLSv1.3 (IN), TLS handshake, Finished (20): * TLSv1.3 (OUT), TLS change cipher, Change cipher spec (1): * TLSv1.3 (OUT), TLS handshake, Finished (20): * SSL connection using TLSv1.3 / TLS_AES_256_GCM_SHA384 * ALPN: server accepted h2 * Server certificate: * subject: CN=www01.yinghli.demo.altostrat.com * start date: Jun 4 10:36:43 2023 GMT * expire date: Sep 2 10:36:42 2023 GMT * subjectAltName: host "www01.yinghli.demo.altostrat.com" matched cert's "www01.yinghli.demo.altostrat.com" * issuer: C=US; O=Let's Encrypt; CN=R3 * SSL certificate verify ok. * using HTTP/2 * h2h3 [:method: GET] * h2h3 [:path: /] * h2h3 [:scheme: https] * h2h3 [:authority: www01.yinghli.demo.altostrat.com] * h2h3 [user-agent: curl/8.0.0] * h2h3 [accept: */*] * Using Stream ID: 1 (easy handle 0x149019a00) > GET / HTTP/2 > Host: www01.yinghli.demo.altostrat.com > user-agent: curl/8.0.0 > accept: */* > * TLSv1.3 (IN), TLS handshake, Newsession Ticket (4): * TLSv1.3 (IN), TLS handshake, Newsession Ticket (4): * old SSL session ID is stale, removing < HTTP/2 200 < server: nginx/1.18.0 < date: Mon, 05 Jun 2023 02:48:43 GMT < content-type: text/html < content-length: 35 < last-modified: Sun, 04 Jun 2023 09:02:16 GMT < etag: "647c5318-23" < accept-ranges: bytes < via: 1.1 google, 1.1 google < alt-svc: h3=":443"; ma=2592000,h3-29=":443"; ma=2592000 < Page on www01 in asia-southeast1-b * Connection #0 to host www01.yinghli.demo.altostrat.com left intact
15. 清理步骤
提供方网络清理步骤
注意:清理步骤仅显示负载平衡器和 PSC 相关配置,不包含 VPC 和混合连接。
通过终端中的单个 Cloud Shell 删除实验组件
gcloud compute forwarding-rules delete consumer-url-forwarding-rule --global gcloud compute target-https-proxies delete consumer-url-target-proxy gcloud compute ssl-certificates delete wwwglobal --global gcloud compute url-maps delete consumer-url gcloud compute backend-services delete consumer-bs --global gcloud compute addresses delete httpspsclb --global gcloud beta compute network-endpoint-groups delete consumerpscneg --region=asia-southeast1 gcloud compute service-attachments delete ilbserviceattach --region=asia-southeast1 gcloud compute networks subnets delete psc-nat-subnet --region=asia-southeast1 gcloud compute forwarding-rules delete https-ilb-psc --region=asia-southeast1 gcloud compute addresses delete ilbaddress --region=asia-southeast1 gcloud compute target-https-proxies delete on-premise-httpsproxy --region=asia-southeast1 gcloud compute ssl-certificates delete www01 --region=asia-southeast1 gcloud compute url-maps delete on-premise-url --region=asia-southeast1 gcloud compute backend-services delete on-premise-service-backend --region=asia-southeast1 gcloud compute health-checks delete on-prem-service-hc --region=asia-southeast1 gcloud compute network-endpoint-groups delete on-prem-service-neg --zone=asia-southeast1-b gcloud compute networks subnets delete proxy-subnet-asia-southeast1 --region=asia-southeast1
16. 恭喜!
恭喜您完成此 Codelab。
所学内容
- 具有混合 NEG 和分布式健康检查的内部 HTTPS 负载平衡器
- 具有内部 HTTPS 负载平衡器的 PSC 服务附件
- PSC 网络端点组设置
- 通过外部 HTTPS 负载平衡器公开 PSC NEG

